Industrialisation et optimisation de systèmes électroniques
De la conception à l’industrialisation, nous sécurisons vos projets
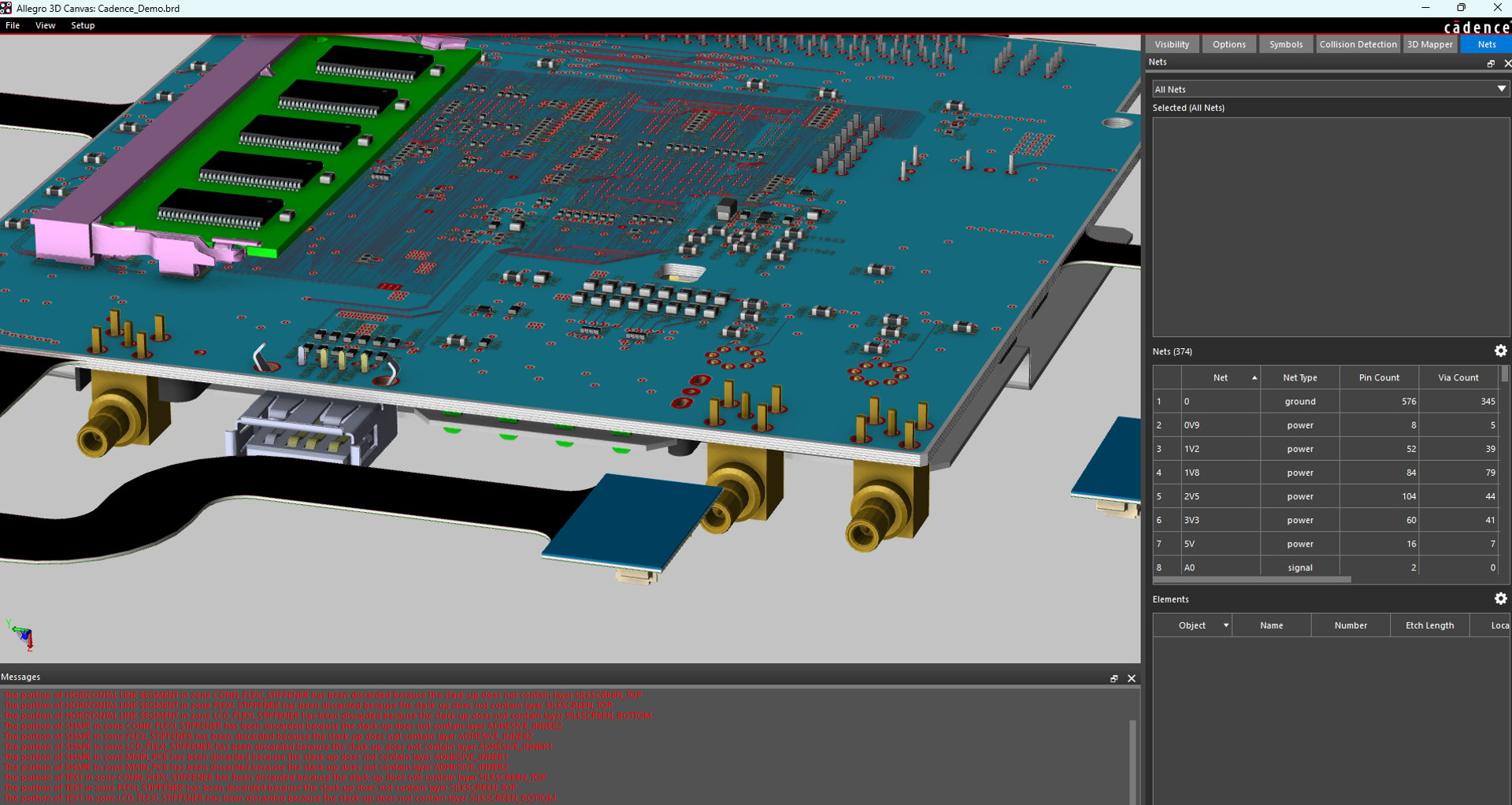
Conception
Optimisation de cartes électroniques complexes
Validation technique et préqualification CEM
Production série et rework
Industrialisation
Production
À propos d'Anthemis Technologies
Anthemis Technologies est une société spécialisée dans l’ingénierie électronique et l’industrialisation de systèmes électroniques à forte exigence technique.
Nous accompagnons nos clients industriels dans la transformation de leurs concepts en produits fiables, manufacturables et conformes aux exigences du marché.
Notre expertise couvre l’ensemble du cycle de vie produit :
conception et optimisation de cartes électroniques complexes (PCB haute densité, contraintes CEM, signaux rapides)
mise au point et validation technique
préqualification CEM en laboratoire interne
rework et amélioration de cartes électroniques
préparation à l’industrialisation et à la production série
Nous intervenons aussi bien sur des développements complets que sur des phases critiques d’un projet : optimisation d’architecture, réduction des coûts, amélioration de la fiabilité ou résolution de problématiques techniques complexes.
Anthemis Technologies s’appuie sur un écosystème structuré :
Weisstronix pour l’architecture électronique, le design hardware et le firmware
des capacités de production électronique intégrées au groupe, permettant une continuité naturelle entre conception et fabrication
Dépanneur Électronique pour les activités de diagnostic et réparation (distinctes du périmètre Anthemis)
Notre approche privilégie la rigueur technique, la confidentialité et l’efficacité opérationnelle, avec un objectif constant : sécuriser les projets de nos clients et accélérer leur mise sur le marché.


Nos services
De la conception à l’industrialisation, nous sécurisons vos projets électroniques.


Anthemis Technologies accompagne les industriels dans la mise en production, l’optimisation et l’adaptation de systèmes électroniques, en assurant la continuité entre conception, validation technique et fabrication.
Problématiques traitées
produit validé mais difficile à industrialiser
coûts de production trop élevés
dépendance à des composants critiques
instabilités en environnement réel
problématiques de compatibilité électromagnétique
nécessité de modifier un design existant

Différenciation
approche orientée terrain et production
capacité d’intervention sur systèmes existants
continuité entre conception et fabrication
maîtrise des contraintes industrielles réelles
environnement technique dédié
Restez informé
Recevez nos conseils techniques et nouveautés

